Introduction
I’ve had several people contact me in the last few months, all with the same issue. They are getting what appears to be pop up messages on their computer. They all tend to be variations on a theme.
One message says their McAfee (or another brand) of anti-virus is out of date, and you need to contact a company to renew as you have a virus.
Another might warn the user has a virus, needs to click a link to get help in cleaning it.
After talking to the people who contacted me, they confirm a few things.
- The are not running the anti-virus software listed in the message.
- They did a scan with their own installed anti-virus, and it showed no viruses found.
- They use Google Chrome as their default browser.
- Chrome is set to re-open the last set of web pages they were using when it launches.
- When they reboot, they get no messages until after they’ve opened up Google Chrome.
What Happened?
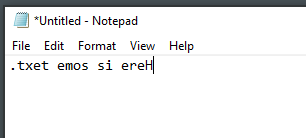
Without meaning to, they went to a website that had code from scammers. They use web programming tricks to create what appears to be pop up messages on their computer. While it looks like the messages are coming from their computer, in reality they are just opening up new web pages.
There is a trick they take advantage of that lets them open up a new Google Chrome window, but it removes the title, tabs, borders, etc. This gives it the appearance of a standard message box.
Let me make one thing clear, I’m not trying to disparage Google Chrome or imply anything negative about it. All of the people who contacted me though were using Chrome, which is why the instructions here focus on it.
How to Fix
Resolving the issue isn’t hard, but does require quite a few steps. Nothing complicated, and well within the capability of even a novice user.
A word of warning first
Understand that if followed exactly, these steps will prevent Google Chrome from opening the last set of web pages you had open automatically.
If there was a page you had opened and need back, at the end I show you how to find them in Chrome’s History so you can reopen them. So the risk is very minimal, again if you follow the instructions exactly.
For my open legal protection though I have to give this warning:
Proceed at your own risk. I offer no warranty or guarantees. Just because these steps works does not guarantee you don’t have a virus as well.
OK, with my cute backside covered, let’s proceed.
First, shut down Google Chrome
If Google Chrome is currently running, follow these steps to shut it down. Alternatively you could do a "hard reset", in other words power your computer off.
If Google Chrome is not running, you should absolutely NOT start it again. Just skip this section and go right to "Prevent it from coming back".
- Right Click in an empty area of the Windows bar at the bottom of you desktop screen.
- Left click once on Task Manager.
- Find Google Chrome in the list. Task Manager has two views, less detail and more.
3a. If you see just a list of a few apps, and nothing else, you are in Less Detail mode. Left click once on Google Chrome. Then left click once on the End Task button in the bottom right.
3b1. If you see a lot of columns displayed, you are in the More Detail view. The left most column is where the applications are listed.
3b2. If don’t see "Apps" at the top, left click the column header once, where it says Name, to sort the data by the list of names.
3b3. Find Google Chrome and left click on it once.
3b4. Left click once on "End Task" in the bottom right of the Task Manager. This should make all the annoying messages go away.
You may be tempted to restart Chrome now, DO NOT DO IT!!! If you do it’ll just start all the fake virus messages back up.
Prevent it from coming back
Preventing this requires several steps, but nothing complicated.
-
Open the Windows File Explorer.
-
Single Left Click once on the View menu at the top.
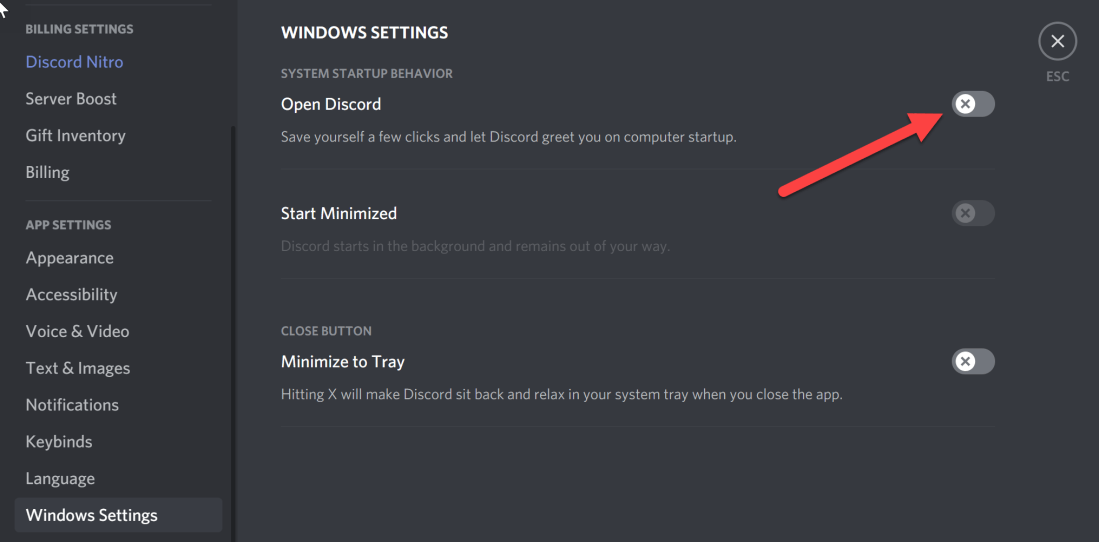
- Toward the right is the Show/hide area. Make sure the box beside "Hidden items" is checked ON.
While you are here, click on the Details button so your screen will give you the most details, and match what you’ll see in the upcoming images. Note as you drill down in the following steps you may need to click Details repeatedly, it depends on how your File Explorer is configured.
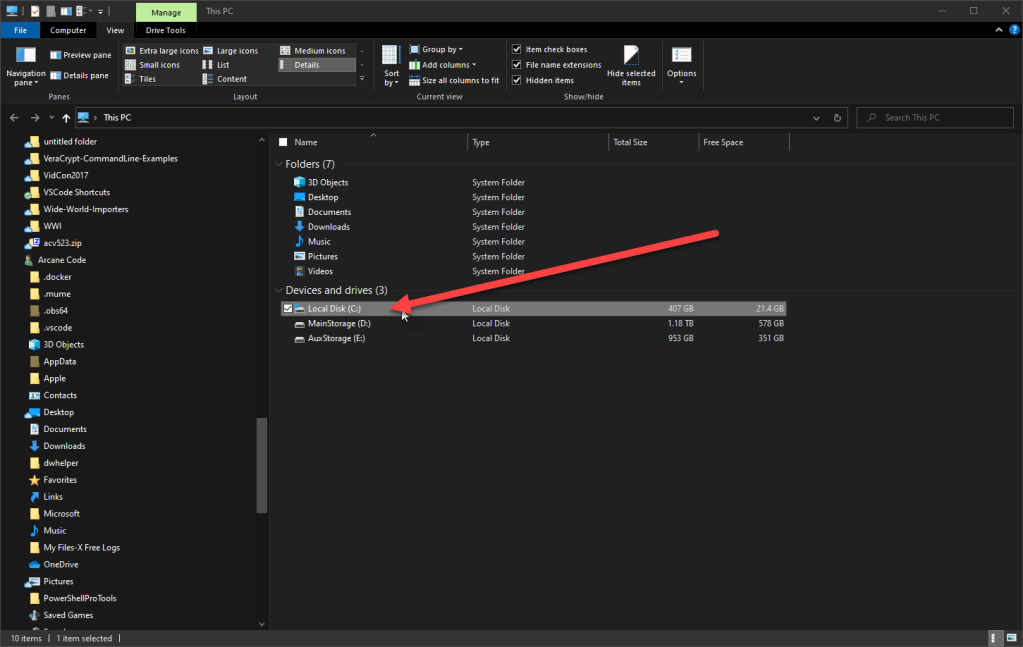
- Now left double click on your C:\ drive.
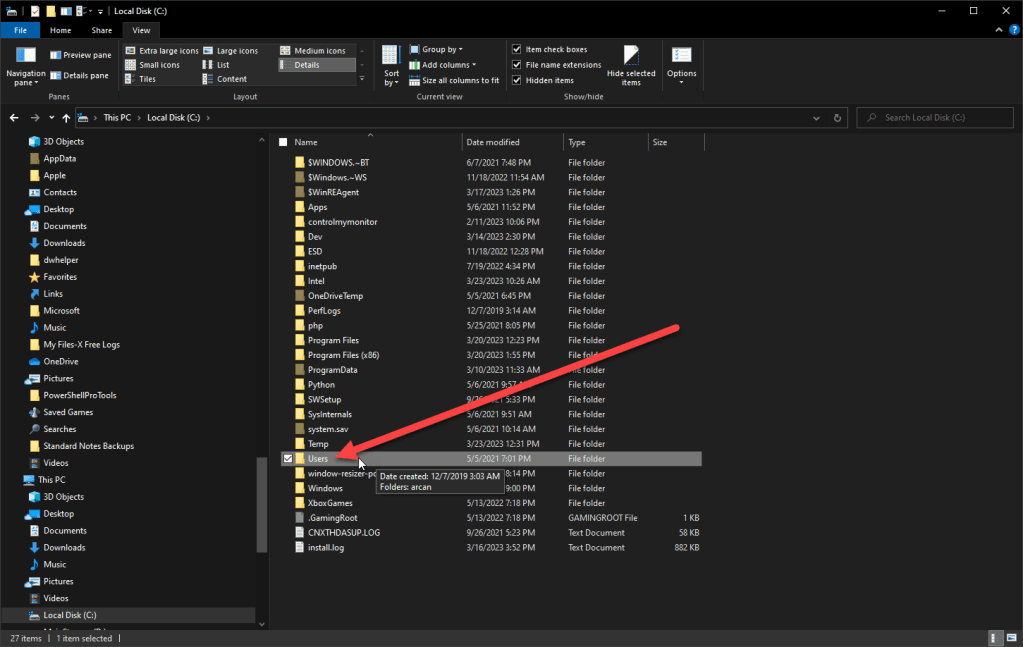
- Scroll down to Users, and left double click on it.
Note, ignore the pop up that has the date created for the folder. That will be different on everyone’s computer.
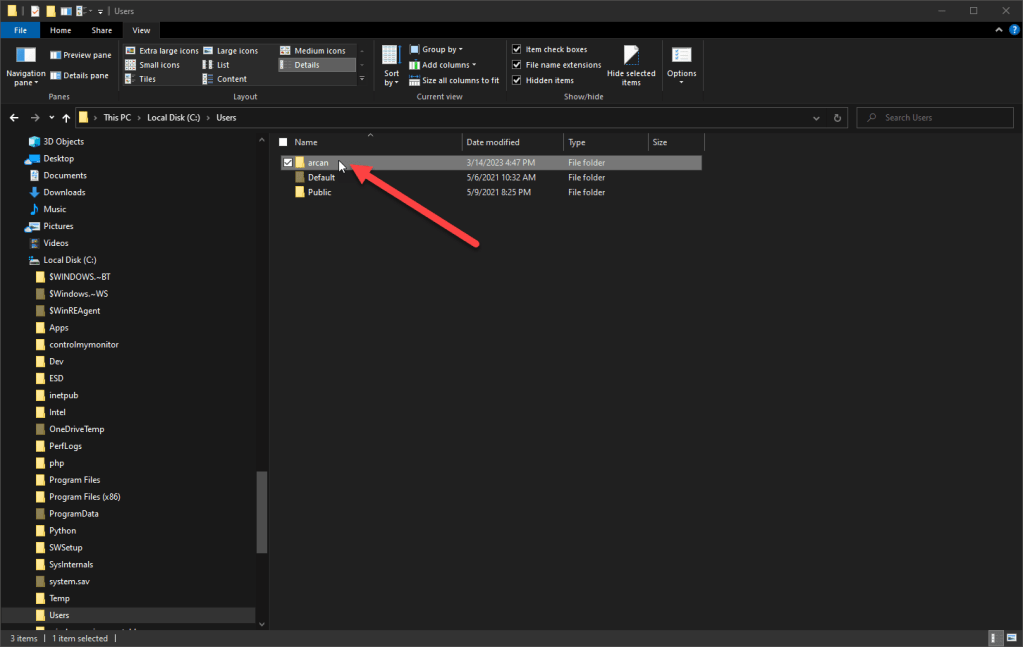
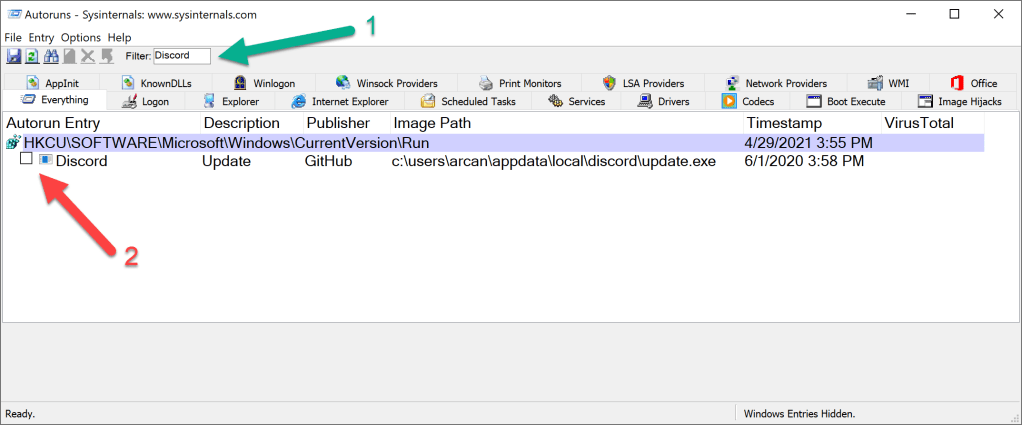
- Find your Windows user name and left double click on it. This will be the abbreviated form of your user name, mine happened to be arcan, use the right one for you.
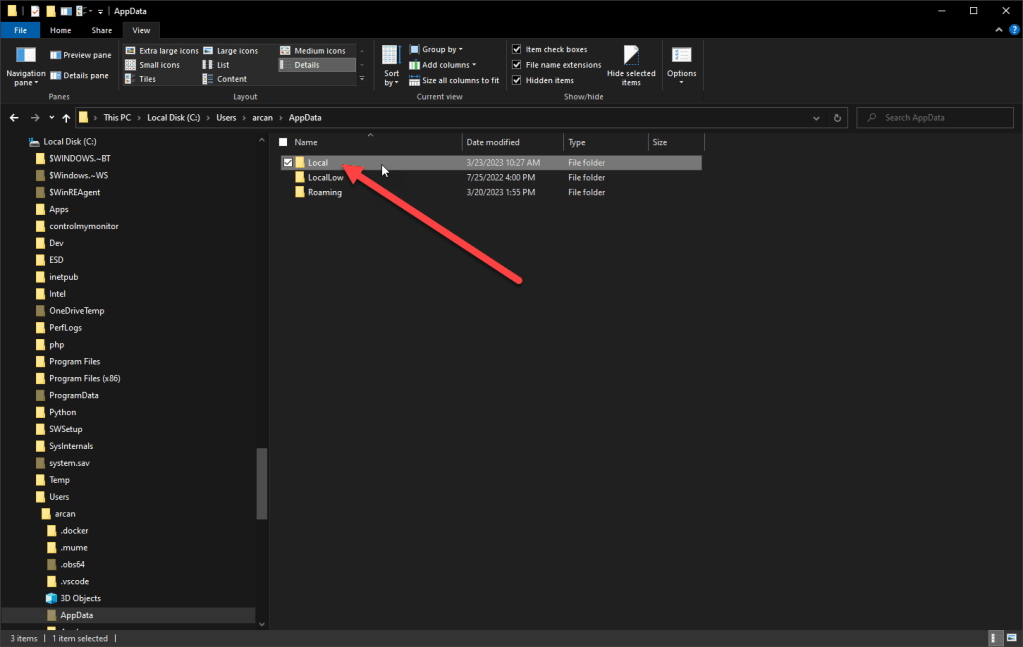
- Now left double click on "AppData". If you don’t see it, it means your Hidden items isn’t checked on, see the instructions in step 3 to make sure it’s checked on.
- Once in the AppData folder, find "Local "and left double click on it.
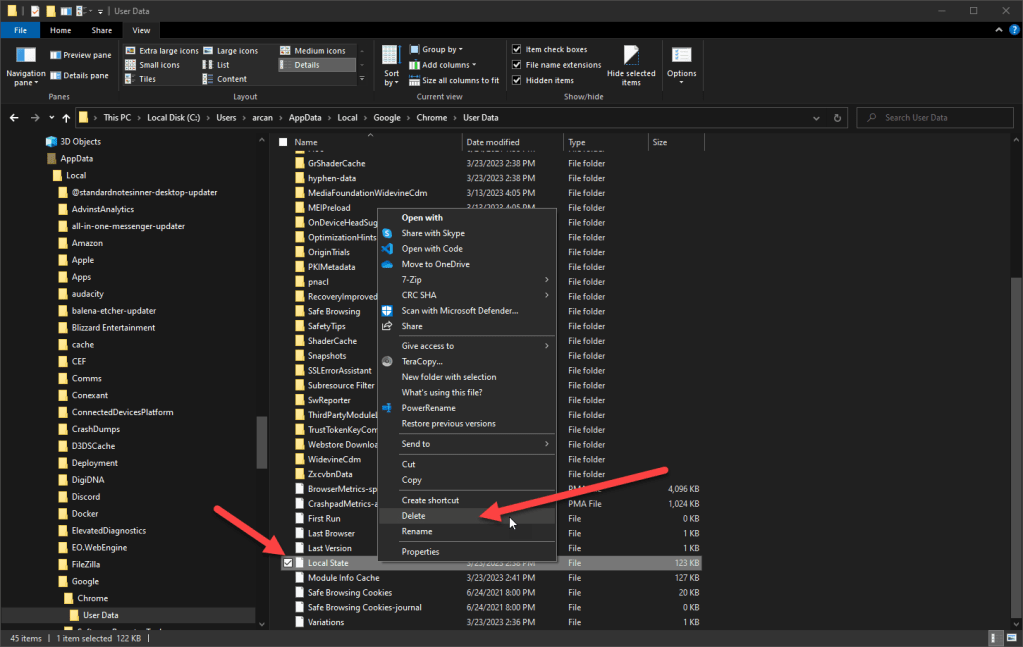
- Find the "Google" and left double click on it.
- Scroll down to "Chrome" left double click on it.
- Almost there! Find "User Data" and left double click on it.
- Find the file (not a folder, but a file) "Local State". Single right click on it and pick Delete in the menu.
You can now close the File Explorer.
-
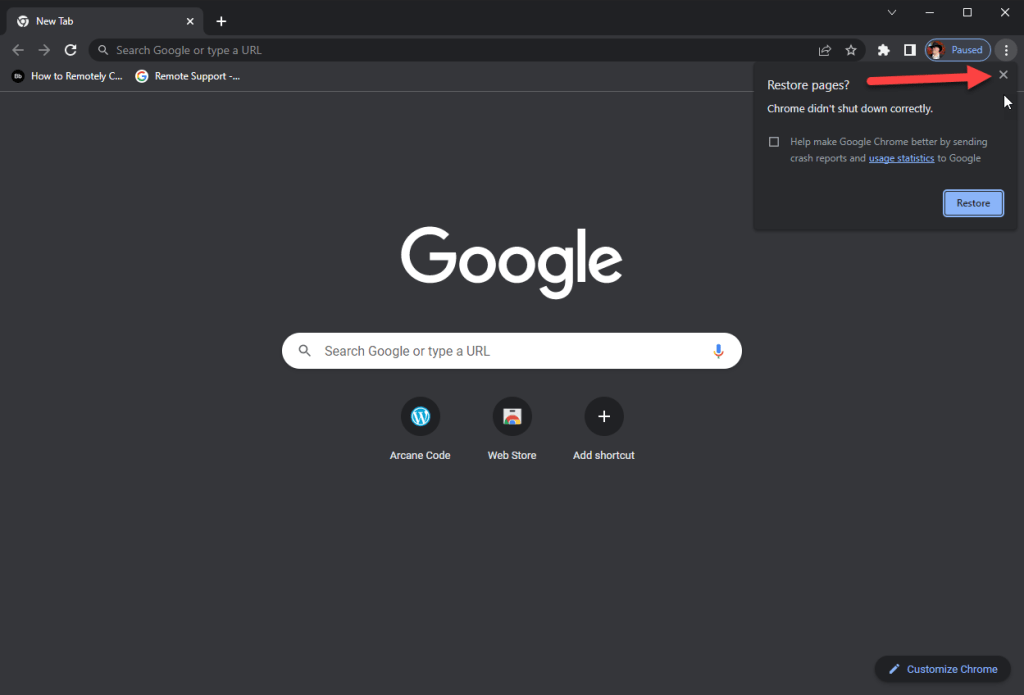
Now you can open Chrome as you normally would.
-
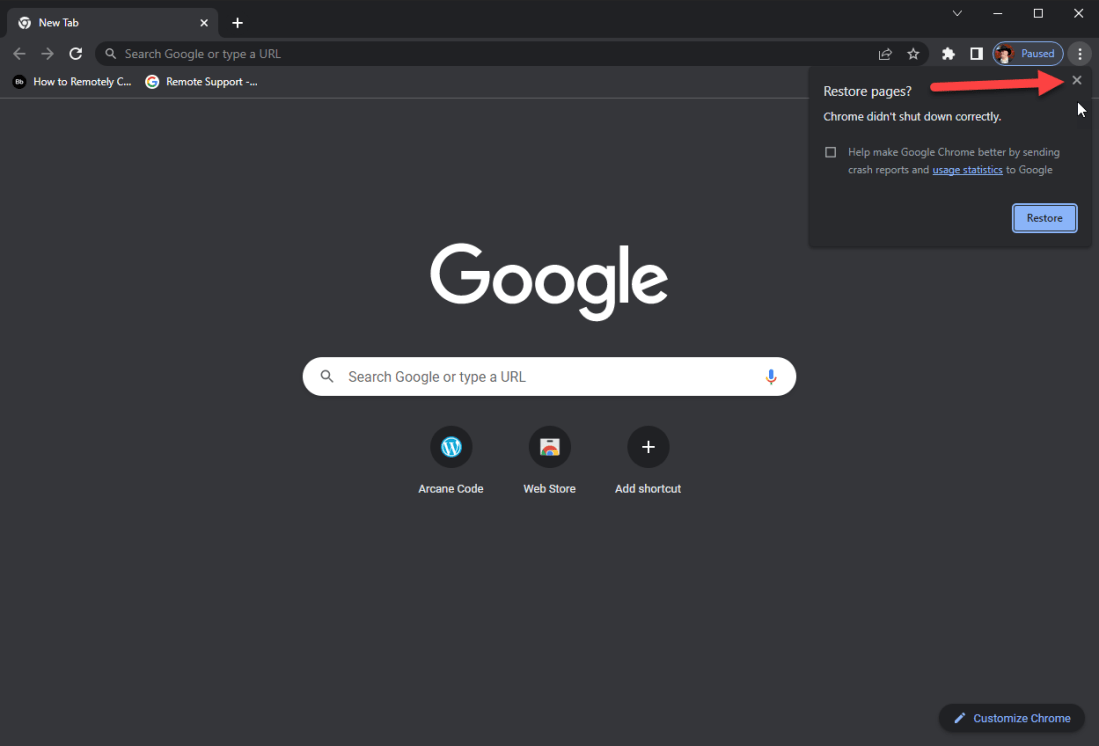
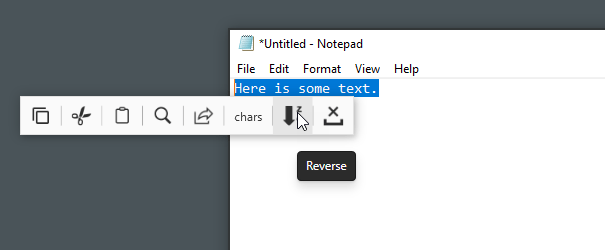
When you reopen Chrome, it will display a little box in the upper right that says "Restore Pages?". Click the X in the upper right corner of the little box to make it go away. Do NOT click on the Restore button or you will be right back where you started.
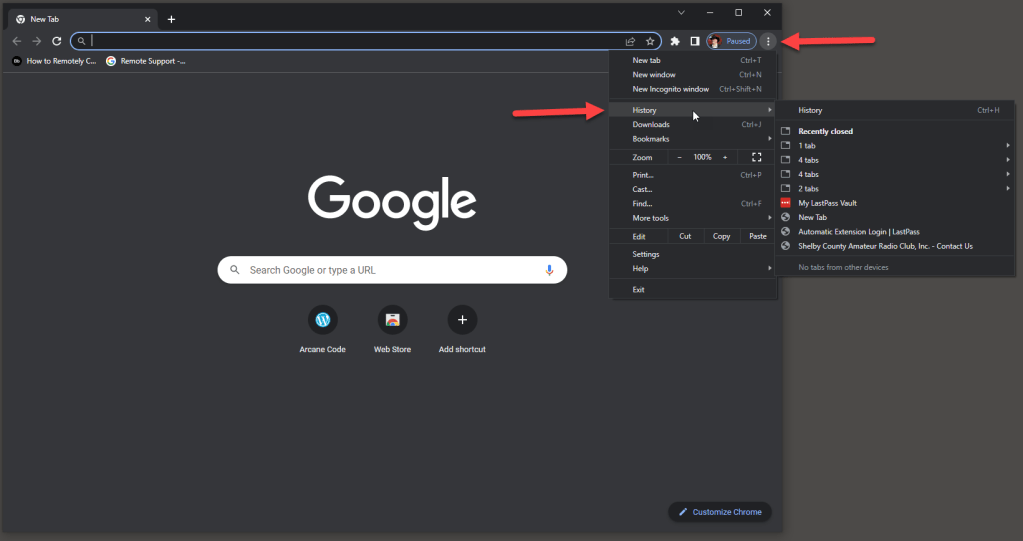
- If there was a web page you had open before and really need back, single left click on the button in the very top right that looks like three periods on top of each other. This will display a menu.
In the menu you can click on History, which then displays tabs from previous sessions. You can navigate this to find the page you need.
BE CAREFUL you don’t open the page that caused the fake viruses before. If you do reopen it by accident you can follow these instructions again, making sure not to reopen the evil website.
I’ll also add it may not be the website itself, but one of the ads that is displayed on the website. Some scammers pay for ads that have evil rotten mean and nasty code in them which creates the fake virus messages. The owner of the actual website you visit may have no idea this is happening.
Conclusion
If you meet the criteria I listed in the introduction, namely you ran your own anti-virus, found nothing, and are using Google Chrome, there’s a good chance you are really the victim of scammers.
Scammers love to prey on people without a lot of computer experience, so I hope the steps here will resolve the issues for you.